What You Can Do to Reduce the Cost of a Data Breach
Category : Cyber Security , Risk Management
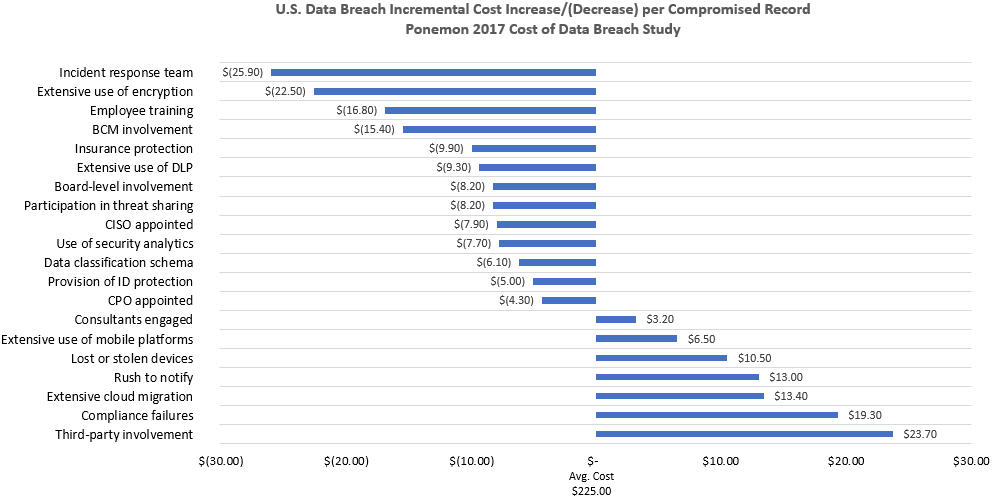
As we note in our Cyber Security services, according to the 2017 Poneman Institute Study, the average cost of a data breach in the U.S. was $7.3M, or $225.00 per compromised record in 2016. The chart below, cited as Figure 7 in the Ponemon Study, illustrates the impact of 20 factors on the per capita cost of a data breach.
Clearly, there are many steps organizations can take to reduce the average cost of a data breach. For example, creating an incident response team could reduce the per capita cost from $225 to $199. The extensive use of encryption, employee training, and business continuity management involvement also significantly reduce breach costs. With respect to insurance protection, it will be interesting to see how the current cost reduction of $9.90 per compromised record will change as the cyber insurance market continues to evolve. According to A.M. Best, the cyber insurance market topped $1 billion in 2016, with more insurers moving to standalone policies. By separating cyber risk from commercial, business interruption, and D&O coverage, carriers will be able to better target and implement exclusionary language. We believe that this will increase insureds’ demand for forensic accounting services to clearly categorize, quantify and validate cyber losses that meet coverage criteria.
On the other end of the spectrum, third-party involvement (customers, suppliers, and other stakeholders in the value chain) represent the highest increase. This is a perennial problem, as organizations struggle with how to most effectively deal with the inherent risk posed by smaller and less sophisticated partners. The Target breach is a good example of this issue. There is only so much organizations can do to inoculate themselves from risks posed by smaller members of their value chain. While they can issue directives and impose stricter security requirements on smaller partners, organizations are not in the business of being cyber security consultants. On the vendor side, supplier diversity programs – as they apply to small business – may take a back seat to security considerations – even at the expense of moving to larger vendors who charge more for their products and services.
Compliance failures, too, continue to be a major thorn in the side of organizations, and data breach costs are just one more manifestation. Compliance systems only work when we humans obey the rules of engagement with those systems. Did you know that six months before its mega breach, Target installed a $1.6 million malware detection system that worked exactly as planned when intruders began stealing PII? However, the company’s security staff ignored the automatic warnings from the system (Fraud Magazine, November/December 2015).